Set permissions
The full Intrexx permissions concept includes the visibility of navigation elements, access to entire applications, as well as access to individual pages, data groups and a distinction by actions (display, create, change, delete) within the applications. In addition to the fixed assignment of authorizations within the application, authorization assignments can also be made accessible via the browser if required. For example, in Intrexx Share, the collaboration application by Intrexx, it is possible to make posts and discussion groups accessible to certain user groups only.
Portal administrator
Once you have created a portal, the portal has a portal administrator. This role is responsible for central actions related to the administration of a portal. See also the Administrators" user group section.
You can create and manage additional portal administrators in the Intrexx Portal Manager after you have logged in to the portal. See also the Manage users section.
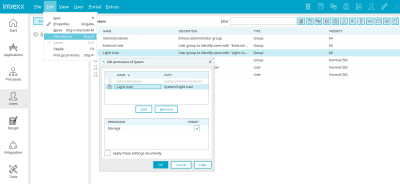
Provide permissions
In Intrexx, permissions can be provided in the permissions dialog which generally always has the same structure.
First column
Displays an image that symbolizes the type of rights holder.
Name" column
Displays the name of the permission holder.
Path" column
Displays the path to the user object in the "User" module.
Add" button
Opens a dialog in which a user object can be selected.
Remove" button
Removes the user object from the list. This does not mean that all of their permissions are automatically removed. The permission holder could still possess permissions by being a member of other objects, e.g. by being a member of the Users group.
Legal" column
When you select a permission holder at the top of the dialog, the individual permissions are displayed at the bottom.
Permit
Activate the respective checkbox to provide the user object with the desired permissions.
Portal access permissions
You can find the portal rights in the main menu under "Portal > Portal rights...".
The menu item is accessible only after logging into a portal. All permissions defined here are valid for the current portal.
Once you have selected the menu item, the "Set portal rights" dialog box is displayed.
Click on a user or user role to display the list of rights.
Below you will find an overview of the portal rights.
Name
| Description |
|---|---|
| Administrate portal | With this right, the portal properties can be configured and portal exports or imports can be created via the main menu "Portal / Export portal" or "Import portal". |
| Configure portal pages in the browser | Rights holders are authorized to administer the portal pages in default mode. |
| Access design module | Rights holders have access to the Design moduleSet design and layout) in the Portal Manager. The right "Access to module design" or the right "Access to module applications" is required to be able to edit the menu structure of the portalEditing the menu structure of the portal). |
| Access module applications | Rights holders have access to the Applications moduleCreate applications) in the Portal Manager. The right "Access to module applications" or the right "Access to module design" is required to be able to edit the menu structure of the portalEditing the menu structure of the portal). |
| Access module processes | Rights holders have access to the Processes moduleCreate processes) in the Portal Manager. |
| Access user module | Rights holders have access to the Users moduleManage users) in the Portal Manager. |
| Intrexx Share Chat | Rights holders can use Intrexx Share Chat. |
Publish Velocity and Groovy scripts | With this right, Velocity and Groovy scripts may be published on the server. |
Manage global language constants | Rights holders can edit language constants in the portal properties / country settings / global texts and in applications. |
Access Integration modules | Automatically activates the "Allow" checkbox for all corresponding portal rights so that they do not have to be selected individually. |
| Run data transfers | Rights holders have the right to carry out data transfers in the Portal ManagerData transfer). |
| Manage FileWalker connections | Rights holders have the right to manage FileWalker connections in the Portal ManagerFileWalker). |
| Manage API keys | Rights holders have the right to manage API keys for the Intrexx Application API in the Portal ManagerIntrexx Application API). |
| Register OData services | Rights holders have the right to register OData services in the Portal ManagerConnector for OData – Consume data). |
| Provide OData services | Rights holders have the right to offer OData services in the Portal ManagerConnector for OData – offer data). |
| Register web services | Rights holders have the right to register web services in the Portal Manager Register web service). |
| Provide web services | Rights holders have the right to offer web services in the Portal ManagerWeb service). |
| Document integration | Rights holders have the right to set up document integration in the Portal ManagerCollaboration - Documents). |
Rights holders have the right to register SAP Gateway sources in the Portal ManagerConnector for SAP Gateway). | |
| Register Lotus Notes sources | Rights holders have the right to register Lotus Notes sources in the Portal ManagerConnector for IBM Lotus Notes). |
| Manage Microsoft Exchange sources | Rights holders have the right to manage Microsoft Exchange sources in the Portal ManagerConnector for Microsoft Exchange). |
| Manage SAP Business Suite sources | Rights holders have the right to manage SAP Business Suite sources in the Portal ManagerConnector for SAP Business Suite - Create connection). |
| Register M-Files services | Rights holders have the right to register M-Files services in the Portal ManagerConnector for M-Files 2.0). |
| Register dg hyparchive services | Rights holders have the right to register dg hyparchive services in the Portal ManagerConnector for dg archive). |
| Access to tools | This setting grants the following rights for functions in the "Tools" module: |
| Use system monitor | Rights holders have the right to use the system monitor in the Portal ManagerSystem monitor). |
| Manage search indexes | Rights holders have access to the Lucene index managementSearch). |
| Manage task scheduler | Rights holders have the right to administer task planning in the Portal ManagerTask scheduler). |
| Manage request variables | Rights holders have the right to manage request variables in the Portal ManagerValidate form and request values). |
| Access email service | Rights holders have access to the e-mail service in the Portal ManagerEmail service). |
User
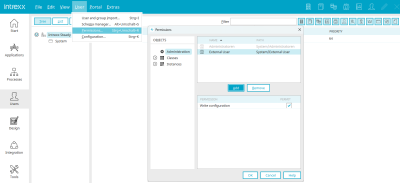
In the "User" module, rights are regulated on two different levels: as global and as individual rights.
Global permissions
Global user rights are controlled via the main menu "Users / Authorizations". Rights holders can, for example, edit object classes and object instances, have access to the schema manager and can add, edit and delete classes or attributes or change the organization chart.
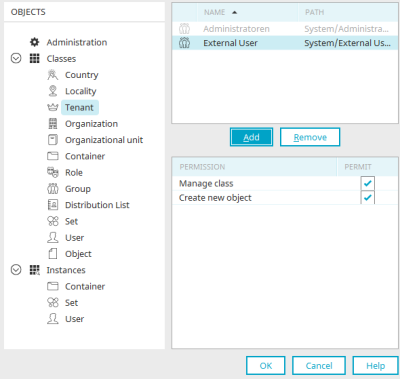
Administration
With the "Write configuration" right, existing object classes can be edited in the schema manager.
Object classes
Manage class
With this right, the currently selected class can be edited in the schema manager.
Create new object
Allows the creation of new objects within the class in the schema manager.
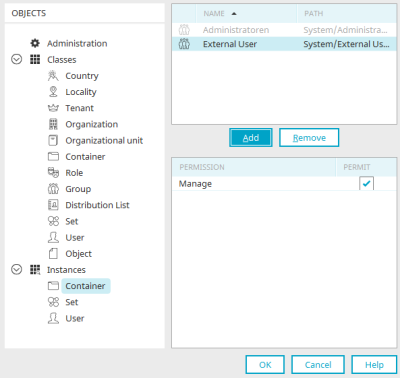
Object instances
Manage
This right applies to instances that are derived from the Container, Set and User base classes. It enables the editing of all taken instances or the respective basic class including the instances from subclasses.
Please note that individual permissions will be overruled when you assign global permissions.
Individual permissions
Individual rights are controlled via the main menu "Edit / Permissions". This main menu can be accessed when a user object is selected.
Add user objects
All information on selecting authorized users in the upper part of this dialog can be found here.
Administrate" right
With the individual permission to edit the properties of individual object instances, you permit the changing of values that are also stored physically in the database for each instance, such as the name of the instance or address or contact data for an instance of the user object.
Apply these settings recursively
With this setting, the "Administrate" right is applied to all objects subordinate to the current user object or is also revoked there if you have deactivated the right in the higher-level, currently selected object.
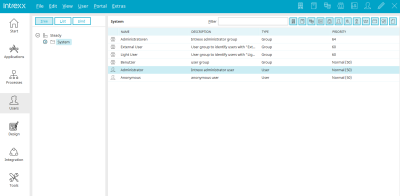
Default users and user groups
The user groups "Administrators" and "Users" already exist in newly created portals. You will also find the users "Administrator" and "Anonymous" there. Information on the rights of these users and user groups can be found here.
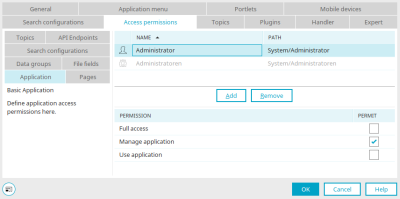
Application permissions
Access rights to applications are defined in the "Applications" module.
Furthermore, the administration permission, which allows the user to edit the application technically, can be provided. The application rights can be edited via the main menu "Application / Authorizations" or the main menu "Edit / Properties" if the application node is selected.
On the left of the dialog, you can see tabs which represent the different levels of access permissions that can be defined for the application:
Application
Access to the application link and the starting page in the browser, administration permissions
Pages
Access to additional individual pages
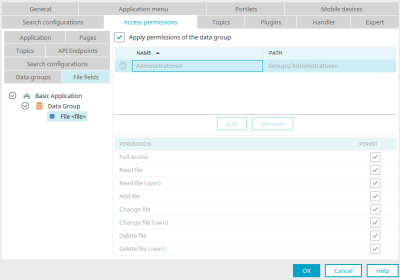
Data groups
Read and write access to application data
File fields
Read and write access to file fields
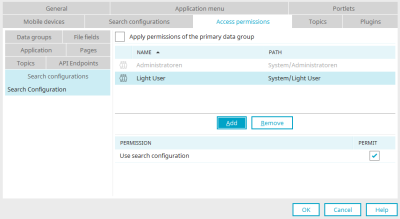
Search configurations
Permissions for search configurations
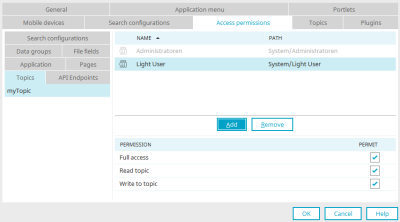
Topics
Permissions for topics
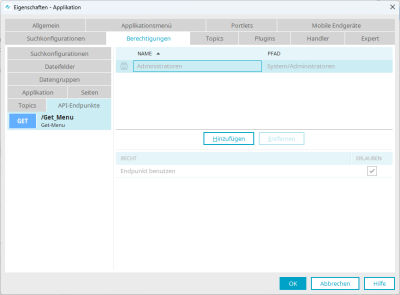
API endpoints
Permission to be able to use the Intrexx Application API.
You can find out how to add rights holders and assign the individual rights in the right-hand section of the dialog here.
New or edited permission settings are transferred to the server when the application is published.
Application
Full access
This setting automatically activates all other permissions.
Manage application
Rights holders are authorized to administer the application in the "Applications" module.
Use application
Permissions holders have access to the application link and the starting page of the application.
The "Administrators" user group has full access to all pages and data groups of the application and the application itself. This setting cannot be changed within the application permissions. Remove the rights holder from the administrator user group if you do not want to grant the right to administer applications. The creator of an application always has permission to administrate the application. This permission will be given automatically to the creator of an application.
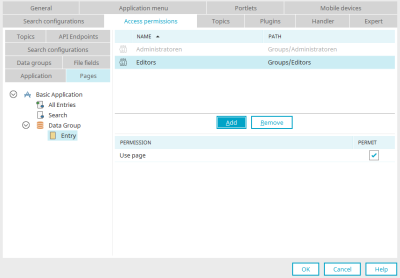
Pages
Allows you to provide access to individual pages of the application. If you select one or more pages in the left-hand area, the rights for these pages can be set in the right-hand area. All pages, which the user does not have permission for, will be automatically hidden from the application menu. Buttons that lead to an unpermitted page will not be shown in the browser.
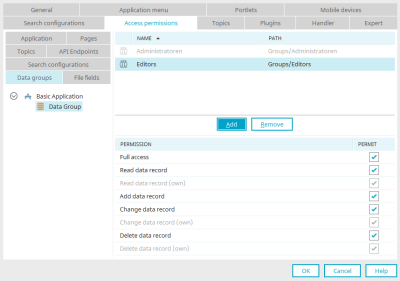
Data groups
Here you will define in which data group data can be read, added to, modified or deleted.
The data group permissions for Intrexx Share are controlled internally with Java classes and cannot be changed here.
Full access
This setting automatically marks all additional permissions.
Read data record
Permissions holders may read the data of an application.
Read data record (own)
Permissions holders may read existing data records they have saved.
Add data record
Permissions holders may add new data.
Change data record
Permissions holders may modify existing data records.
Change data record (own)
Permissions holders may modify existing data records they have saved.
Delete data record
Permissions holders may delete existing data records.
Delete data record (own)
Permissions holders may delete existing data records they have saved.
File fields
If file data fields have been created in a data group, the rights
Full access (enables all permissions named below)
Read file
Read file (own)
Add file
Change file
Change file (own)
Delete file
Delete file (own)
be issued. To do so, select the corresponding file field in the application structure in the left-hand area of the dialog.
Apply permissions of the data group
With this setting, all rights configured for the data group are applied to all file fields contained in it. The rights for individual data fields can only be set if this setting is not active.
If separate authorizations are assigned for an individual file field, a conflict check is carried out. The authorizations for which a conflict has been detected are highlighted in red in the authorization table. A conflict occurs when permissions to a file field are assigned that, according to the data group, are not permitted. If, for example, a user is only allowed to read in the data group, but is granted delete permission for a file field in this data group, a conflict occurs. The ""Delete"" permission will then be highlighted in red.
Search configurations
Select the search configurations, you would like to define the permissions for, on the left-hand side of the dialog.
Apply permissions of the data group
This setting applies the rights of the data group that you have selected in the search configuration settings.
Topics
"Topics" are related to websockets. They represent the object that WebSocket messages output/make available. A topic can be subscribed to by a "consumer". A topic can be compared to a message channel that can be subscribed to.
You can grant the following permissions for topics:
Full access
If you select this option, the corresponding user has the rights "Read topic" and "Write to topic".
Read topic
With this permission, you can control which users should be able to see WebSocket messages in the browser.
Write to topic
This permission refers to the user of a process that contains a WebSocket action or a Groovy action with WebSocket functions. You can execute processes in a user context. The permissions of the respective user are relevant in this case. If the user does not have the "Write to topic" right, then no WebSocket message is sent to the topic via the process and is also not displayed in the browser.
More information about WebSockets is available here:
API endpoints
This displays the API endpoints that you have created within the application. You can select one or more API endpoints and then assign a user or a user group.
For more information on assigning rights to API endpoints, see section Assigning a user to an API endpoint.
Further information on the Intrexx Application API can be found in the Intrexx Application API section.
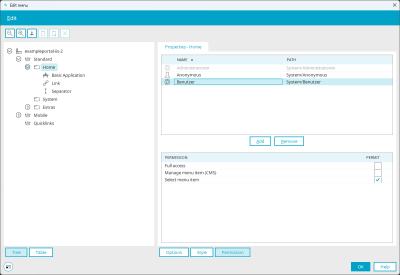
Menu structure
Permissions can be assigned for each menu item. These rights can be edited via the main menu "Portal / Edit menu structure". Menu items that a user may not select will be hidden in the browser.
The "Manage menu item (CMS)" right enables the publication of articles from the CMS application in this menu item. Articles are published directly in the CMS application. For menu items that originate from the CMS, the permissions cannot be managed via the menu designer. Deleting a CMS menu item is also only possible via the CMS application. Menu items that refer to CMS content can only be managed in the CMS application.
The "Select menu item" right allows the corresponding users to select the menu item in the browser.
With the "Full access" right, all rights are automatically marked as "Allowed" and thus also granted by clicking on "OK".
You can find more information on the topic "Edit menu structure" here.
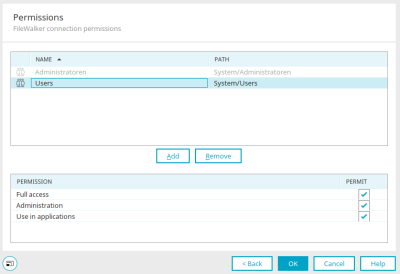
FileWalker
Rights for accessing files in the network are regulated in two places: In the connection in the "Integration" module and in the properties of the FileWalker element in the "Applications" module.
Granting rights in the "Integration" module
You can find out how to add users to the list of authorized users here.
Full access
This setting automatically activates all other permissions.
Administration
With this permission, the settings of the connection can be administrated.
Use in applications
Rights holders are authorized to select the connection in the "Applications" module and assign it to a FileWalker element.
Please note that permissions for FileWalker connections are subordinate to the directory permissions of the individual users.
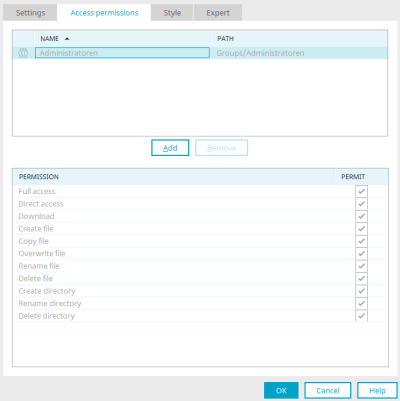
Granting rights in the "Applications" module
The rights for the "FileWalker" application element are granted on the "Rights" tab in the properties dialog.
You can find out how to add users to the list of authorized users here.
Full access
This setting automatically marks all additional permissions.
Direct access
The permissions holder has direct access to all files. Changes will be applied to the original files.
Download
Download files.
Create file
Create new files.
Copy file
Create copies of a file.
Overwrite file
Overwrite files.
Rename file
File names can be changed.
Delete file
Files can be deleted.
Create directory
Additional network directories can be created.
Rename directory
Directory names can be changed.
Delete directory
Directories can be deleted.
Activate the desired rights by activating the corresponding checkbox in the "Allow" column. FileWalker users also require rights to the application and to the page containing the FileWalker element.
Web service
To be able to configure web services, the portal rights "Register web services" and access to the "Tools" module must be granted.
Implement a login module
All information on this topic can be found here.
Generic permissions
Requirements
To be able to call up Generic Rights Management, the "Activate options for experts" checkbox must be activated under "Extras > Options > Portals".
Target audience
Generic rights management is designed for experts who want to manage additional rights beyond the dialog-supported assignment of rights. To use the function, it is helpful if you are familiar with "Java Permission Classes".
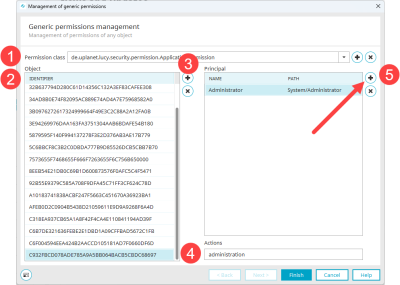
Functional description
With the Generic rights management, you have the option of assigning the rights classes provided by Intrexx and your own rights classes to specific objects. You can then assign the objects to rights holders. You can specify which actions are to be executed in each case. Later, you can use Groovy, for example, to query at runtime whether a specific rights holder is allowed to perform a specific action for a specific object and react accordingly.
The following is an example of how to add a (further) rights holder to an Intrexx rights class and how to add an additional right.
Use Intrexx rights classes - Add rights holder
Step-by-step guide
To add an (additional) rights holder to an Intrexx rights class, proceed as follows:
Open the "Rights class" selection list.
The rights classes provided or used by Intrexx are displayed.
You can find information on Intrexx rights classes under the following links:
Select the desired rights class (
 ).
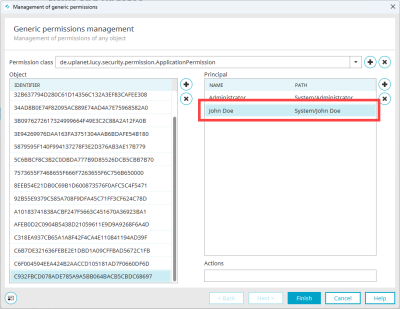
).In the screenshot below, the permission class de.uplanet.lucy.security.permission.ApplicationPermission has been selected.
All objects (applications) that use this rights class are displayed in the "Object" area (
 ). In this case, the identifier is the GUID of the respective application.
). In this case, the identifier is the GUID of the respective application.As soon as you select an identifier, the rights holders are displayed in the "Rights holder" area (
 ).
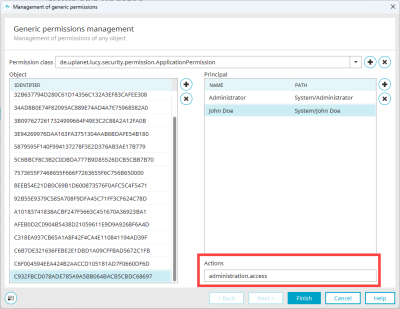
).As soon as you select a rights holder, the permitted actions are displayed in the "Actions" field (
 ). The "Actions" field is an input field. Here you can add or remove actions (separated by commas).
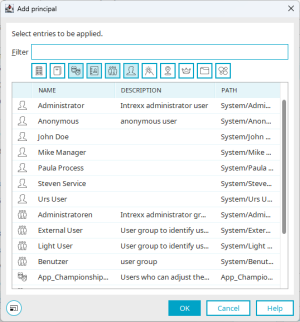
). The "Actions" field is an input field. Here you can add or remove actions (separated by commas).Click on the
 icon.
icon.The "Add rights holder" dialog box is displayed.
Select the desired rights holder.
The rights holder is displayed.
Enter the desired rights in the "Actions" field.
The screenshot below shows the rights administration,access.
Click on "Finish".
More information
Add your own rights classes
Step-by-step guide
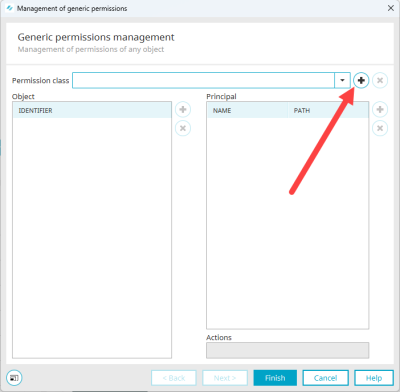
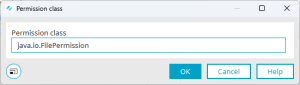
To add your own or a new rights class, proceed as follows:
Click on the
 icon.
icon.The "Rights class" dialog box is displayed.
Enter the rights class.
In the screenshot below, this is java.io.FilePermission.
Click on "OK".
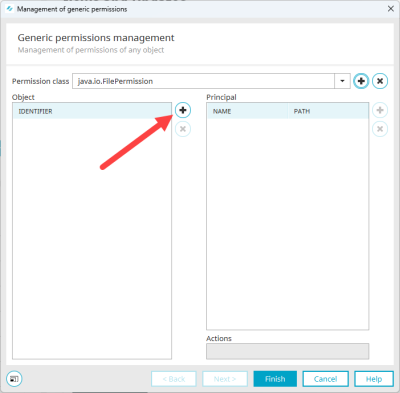
You return to the "Generic rights management" dialog box.
The recorded rights class is displayed.
Click on the
 icon.
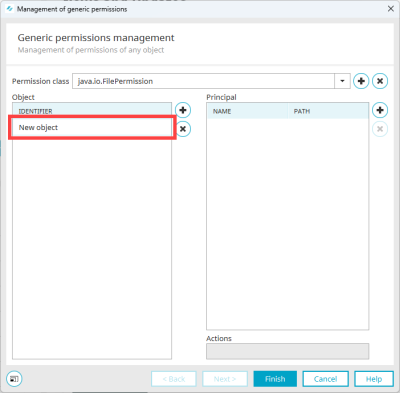
icon.A new line is displayed in the "Object" area.
Click in the new line and enter the identifier.
In the screenshot below, this is a path to a file.
(Compare Class FilePermission
 .)
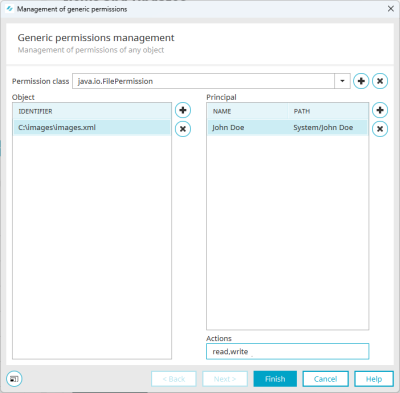
.)Click on the
 icon in the "Rights holder" area.
icon in the "Rights holder" area.The "Add rights holder" dialog box is displayed.
Select the desired rights holder.
You return to the "Generic rights management" dialog box.
The rights holder is displayed.
Enter the desired rights in the "Actions" field.
The screenshot below shows the read,write rights.
Click on "Finish".
More information